Former MI6 chief hacked by Russian security services

The former head of MI6 and a Cabinet minister had their emails stolen by Russian intelligence as part of a Kremlin campaign to undermine British democracy, it has emerged.
The Russian Federal Security Service (FSB) launched cyber attacks on hundreds of MPs, peers, senior officials and journalists in an attempt to meddle in UK politics, a senior foreign office minister has said.
Leo Docherty told the House of Commons that the Government had sanctioned two Russians, including a senior FSB agent, in connection with the cyber attacks.
He said the spies had worked inside the FSB’s Centre 18 and for a hacking group named “Star Blizzard”.
Among the victims was Sir Richard Dearlove, the chief of MI6 between 1999 and 2004, who said his emails were compromised after a friend’s account was hacked in 2020.
Sir Richard’s messages were leaked online and doctored in an effort to allege a conspiracy to bring down the Brexit withdrawal agreement.
He said the Government had recently approached him to tell him he had been a victim of the Russian state hackers.
“I think the Government has now got so many incidents they thought it was time to go public,” he said.

Star Blizzard was also responsible for the theft of US-UK trade documents from Liam Fox, the then international trade secretary.
The documents were subsequently leaked publicly prior to the 2019 general election, and used by Jeremy Corbyn, the then Labour leader, to claim “the NHS is on the table and will be up for sale”.
The documents, it later emerged, had been circulating online and been shared by anonymous accounts on Reddit and Twitter, having apparently been stolen and then leaked by Russian agents.
In 2020, Reuters reported they had been hacked from an account used by Dr Fox.
Russia’s ambassador in London was summoned by Lord Cameron, the Foreign Secretary, to explain the industrial-scale attempt to interfere with UK democracy. Russia sent a deputy in his place.
Mr Doherty told MPs Russian hackers had “targeted members of this House… they have been targeting civil servants, journalists and NGOs”.
“They have been targeting high-profile individuals and entities with a clear intent – using information they obtain to meddle in British politics.”
The Foreign Office said it would be sanctioning Ruslan Peretyatko, a Russian FSB intelligence officer, and Andrey Korinets, a member of Star Blizzard. The Russian embassy called the sanctions “illegitimate unilateral restrictions”.
The US Department of Justice said it would be offering up to $10million (£7.9m) for further details on the alleged hackers.
In court filings, the US accused the pair of targeting American defence and energy officials, as well as intelligence officers, and of hacking attacks in Ukraine.
The hackers gained access to victims’ emails by “spear phishing” – a technique that uses subterfuge to deceive targets into revealing sensitive information or login details.
Such scams could include setting up fake email addresses, designed to look like those of real politicians, academics or military officials, and attaching fake PDF files or websites that could be used to hack victims.
The attacks originated from within the FSB, formerly known as the KGB, from a body known as “Centre 18”.

The hacking efforts have been underway since at least 2015 and targeted multiple political parties.
Other victims included Chris Donnelly, the director of the Institute for Statecraft, a UK think-tank which had initiatives to defend democracy against Russian disinformation in 2021.
Western security officials said all known victims had been warned, and that GCHQ’s National Cyber Security Centre planned to issue further guidance to senior level individuals at risk of future hacks.
Lord Cameron said Russian efforts to interfere with British politics had “failed”, adding: “Russia’s attempts to interfere in UK politics are completely unacceptable and seek to threaten our democratic processes. Despite their repeated efforts, they have failed.”
Oliver Dowden, the Deputy Prime Minister, added: “We will continue to call this activity out, to raise our defences, and to take action against the perpetrators.”
The centre of the hacking operation is a drab city in the Urals almost 1,000 miles northeast of Moscow. Within the Arctic Circle, a bodybuilder working for Russia’s FSB intelligence service had been quietly running a campaign to undermine British democracy.
Over the past eight years, Andrey Korinets, a cyber hacker, targeted hundreds of MPs, peers, senior Government officials, academics, journalists and the former head of MI6.
Finally on Thursday, intelligence agencies in the UK working with counterparts in the US decided to call Mr Korinets out.
Mr Korinets, they said, was a member of a cyber hacking operation given the rather glamorous, sci-fi sounding name Star Blizzard. Mr Korinets was placed on a UK sanctions list by the National Crime Agency.
Simultaneously, the US Department of Justice indicted him on a series of hacking charges and offered a $10 million bounty for his whereabouts.
His handler inside the FSB, the post-Communist successor to the KGB, was identified by UK and US authorities as Ruslan Peretyatko, an FSB intelligence officer and member of Star Blizzard.
The two men are part of a team based inside Centre 18, a unit within the FSB, which runs its cyber espionage operations targeting the UK.
Centre 18’s aim was to “interfere in UK political processes”.

With a general election looming, British intelligence officers fought to confirm the Centre 18’s and Star Blizzard’s role in the attempted – and occasionally successful – hacking of politicians and senior figures.
They also tried to identify two of the group’s leaders.
Mr Korinets makes an unlikely spy in many ways. Reuters news agency had identified Mr Korinets through a trail of digital breadcrumbs that linked him to computer servers used by the FSB.
He had a profile on a dating website, which was recently deleted, as well as a portfolio on an IT work website, which included a link to a shop to buy steroids and a fan site for a Russian queen of figure skating.
Online photographs show Mr Korinets with muscles bulging in a tight-fitting black T-shirt in the gym. A website suggested he can bench press almost 300lbs while his one-time Twitter account had concentrated mainly on pigeons and domain registration.
Mr Korinets – who used the cyber moniker Zombiexe – had confirmed to Reuters that he owned relevant email accounts linked to cyber attacks but denied he worked for offshoots of the FSB.
He admitted to Reuters he had been caught up in cyber crime and hauled through the courts in Russia some years ago. It is possible the FSB then recruited him.
Reuters had linked Mr Korinets to cyber attacks on three nuclear research labs in the US in 2022 through a Russian hacking team called Cold River.
The reality is Star Blizzard, Cold River and groups known as Callisto, Seaborgium, are all one and the same.
The Telegraph understands that the groups operate out of Syktyvkar, a city in the Urals inside the Arctic Circle, where the FSB has a regional branch that has oversight of spying on Nato.
To the untrained eye the city is a non-descript centre that makes money out of the oil fields to the north.
What Star Blizzard has been up to was disclosed in an extraordinary statement made to parliament by Mr Docherty, the Minister for Europe.
He said the FSB and Star Blizzard had “selectively leaked and amplified information” since 2015, conducting “spear-phishing” cyber attacks to steal information from a “significant” number of parliamentarians from multiple political parties.
He added that impersonation attempts and “false accounts” had been made to compromise email accounts in the public sector and wider civil society to create a “believable approach seeking to build a rapport before delivering a malicious link”.
While the Government insisted the FSB had failed in its attempts at interference, the reality is it has had success in stealing information and hacking accounts.
Mr Docherty told MPs Star Blizzard had been behind the leak of trade documents used by Mr Corbyn in the run up to the election he lost to Boris Johnson.
Mr Docherty also linked the FSB’s Centre 18 activities to a 2018 hack into the Institute for Statecraft.
Christopher Donnelly, the Institute’s founder, also had his email account compromised in December 2021.
In both instances, stolen documents were subsequently leaked online.
The Institute’s website remains essentially out of action, all its data removed pending an investigation into the theft.
Based on the leaks, a Scottish newspaper accused the institute of being a “shadowy” think tank that was funded by the Foreign Office.
Sir Richard Dearlove, the former head of MI6, told The Telegraph on Thursday that his emails, using the email service ProtonMail, had been hacked in a cyber attack in May last year. The stolen emails were sent in 2018.
“They got into the ProtonMail account of my colleague,” Sir Richard said, referring to an academic with whom he reportedly campaigned for a tougher Brexit deal than the withdrawal agreement being negotiated at the time by Theresa May.
He said: “He and I were involved in Brexit and as a result they got all my Proton emails off his computer and made it look like they had hacked my computer.”
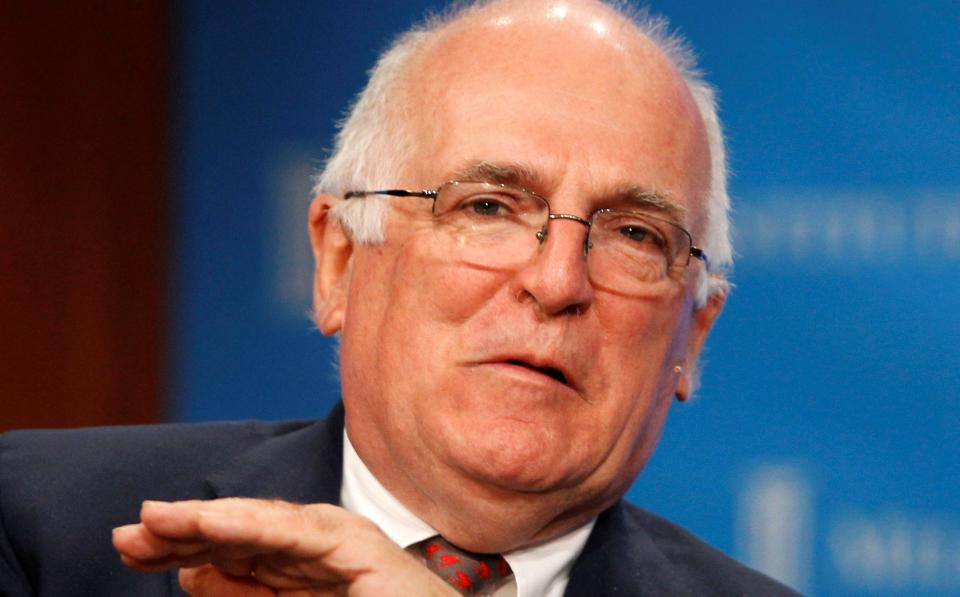
Those emails, said the former spymaster, were passed by the hackers to a pro-Kremlin supporter and then “twisted all over the place to make it look as though I was a svengali behind a conspiracy to bring down the [EU] Withdrawal Agreement.”
He added: “It seems pretty clear some of the material had been doctored.”
Investigators had linked the hack to Cold River, an alternative name for Star Blizzard.
Cyber security experts who have studied Centre 18 and its spin off cyber gangs said the group had been in operation since 2015.
‘It’s an intelligence game’
Rafe Pilling, head of cyber security company Secureworks’ Counter Threat Unit, said: “We’ve seen them targeting politicians, diplomats and NGO-type organisations.
“Predominantly it’s an access-for-intelligence game with them as they engage in influence operations and leak stolen information into the public domain.”
The decision to call out Centre 18 was taken following discussions within the Five Eyes, the intelligence services of the US and UK as well as Australia, Canada and New Zealand.
It is understood Five Eyes’ heads discussed the Russian cyber threat at a meeting in California in November, attended by Ken McCallum, the MI5 director general, along with FBI director Christopher Wray.
In a statement on Thursday, Paul Chichester, the director of the National Cyber Security Centre, said: “Russia’s use of cyber operations to further its attempts at political interference is wholly unacceptable and we are resolute in calling out this pattern of activity with our partners.”
Cyber security professionals have tracked the gangs with their various aliases for some years. It is only now they have been directly attributed to the Kremlin’s security apparatus.
While dubbed “Star Blizzard” by UK officials, Microsoft security experts dubbed the group “Seaborgium”, while Google hunted them as “Cold River”.
Ukraine’s security forces, meanwhile, believe Centre 18 is also behind another hacking group, that it labelled “Armageddon”, operating out of Sevastopol in Crimea, specifically targeting Kyiv’s operations.

 Yahoo News
Yahoo News 
